CVE-2026-25253 turned 42,665 self-hosted OpenClaw agents into one-click remote code execution targets, with 93.4 percent authentication bypass, 800 malicious skills already sitting inside ClawHub at disclosure, and a 24-hour patch to v2026.1.29. CVSS 8.8 HIGH, CWE-669, disclosed by Oasis Security in early May 2026. This is the first agent-era security crisis at scale, and the structural lessons land harder than the bug itself.
The fix is already shipped. What is not fixed is the model. OpenClaw's WebSocket gateway listened on localhost, treated browser JavaScript as trusted because the origin was loopback, and auto-submitted its own auth token when a malicious gatewayUrl query string asked it to. None of that is unusual for self-hosted agent runtimes in 2026. It is, in fact, close to the default. Which is why CVE-2026-25253 reads as a preview of the agent-ecosystem CVE class we are going to see a lot more of, not a one-off.
We have spent the last week reading the SecurityWeek and NVD writeups against the patch diff, watching the Censys exposed-instance count more than double, cross-checking the ClawHub malicious-skill sweeps, and comparing the OpenClaw attack chain against how other agent runtimes route trust. The conclusion is uncomfortable. The agent-era security model is fragile in ways the post-incident discourse is not yet pricing correctly. This piece lays out what happened, what the numbers mean, what the structural failure was, and what we expect to break next.
TL;DR: the agent-era's first scaled CVE in one minute
CVE-2026-25253 is a one-click RCE in OpenClaw (also tracked as clawdbot and Moltbot) before version 2026.1.29. A malicious website opens a WebSocket to ws://localhost on the OpenClaw default port, passes a gatewayUrl query string, and the agent connects to the attacker's server while auto-submitting its own session token. No user prompt, no rate limit on loopback connections, no review gate between the page and the agent's authentication state. CVSS base score is 8.8 (AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H). Weakness class is CWE-669, incorrect resource transfer between spheres.
The headline numbers we are tracking, all sourced from public defender community telemetry and vendor disclosures in the week of May 11 to May 15, 2026:
- 21,639 → 42,665 internet-reachable OpenClaw instances as Censys updated its scan signatures in the 72 hours after disclosure — the higher number reflects improved visibility, not new deployments.
- 93.4 percent authentication bypass rate across the reachable population per Oasis Security and follow-on sweeps, meaning roughly nine in ten agents would accept the chain without firing a user-confirmation prompt.
- ~800 malicious or suspicious skills identified inside the ClawHub registry by defender community pulls, against a registry total of roughly 4,000 — the 20 percent figure that has been circulating.
- Patch v2026.1.29 shipped within 24 hours of the private disclosure, closing the auto-submit path and adding pairing rate limits.
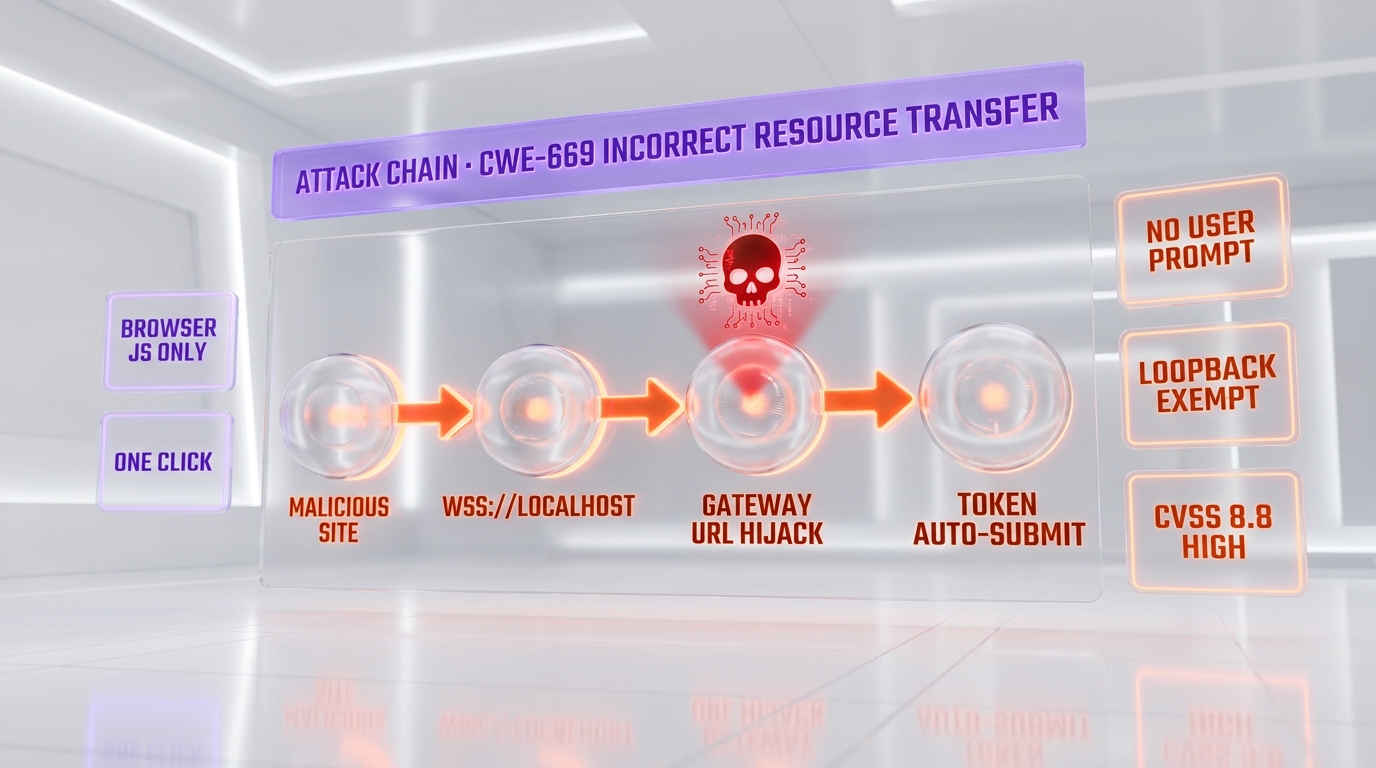
The attack chain, decomposed step by step
The technical chain is short, which is exactly why it ended up affecting tens of thousands of instances. There are no novel primitives; there is no zero-day in the WebSocket protocol; there is no clever sandbox escape. There is a sequence of three reasonable-looking design choices that compose into a one-click RCE.
Step 1 — Browser opens WebSocket to localhost without origin checks
Browsers do not enforce cross-origin restrictions on WebSocket connections to loopback addresses the same way they do for fetch and XMLHttpRequest. A page on attacker.example can open ws://localhost:PORT and the browser will let the handshake proceed. This is not a browser bug. It is the documented behavior, and it predates the agent ecosystem by a decade. What changes in 2026 is what is listening on localhost.
Step 2 — OpenClaw accepts a gatewayUrl from the query string
The OpenClaw gateway accepted a gatewayUrl parameter passed in the WebSocket handshake query string and treated it as the authoritative target for the agent's outbound control connection. Per the NVD entry: "OpenClaw (aka clawdbot or Moltbot) before 2026.1.29 obtains a gatewayUrl value from a query string and automatically makes a WebSocket connection without prompting, sending a token value." The phrase that does the damage is "without prompting." No human confirmation. No origin check. No allow-list for gateway URLs.
Step 3 — Token is auto-submitted to the attacker gateway
Once the agent connects outbound to the attacker-controlled gateway, it submits its own session token as part of the handshake. The attacker now has authenticated control of a self-hosted agent running with the user's privileges. From there, shell command execution, file read, credential exfiltration, and pivot to other connected services are all standard agent-runtime capabilities being used against the user instead of for them.
Step 4 — Loopback exemption removed the brake
The OpenClaw rate limiter exempted loopback connections from throttling — a reasonable default for local-only services, and disastrous for a service that turned out to be reachable from any browser tab. Combined with auto-approval of localhost-originated pairings, the brake that should have caught the attack chain on the second or third attempt never fired.
None of these four choices is wrong in isolation. Each is a reasonable assumption inside the threat model the OpenClaw team was working with three years ago, when self-hosted agents were a developer hobbyist space. They become catastrophic when the population scales past 40,000 instances and the runtime starts holding credentials for production services.
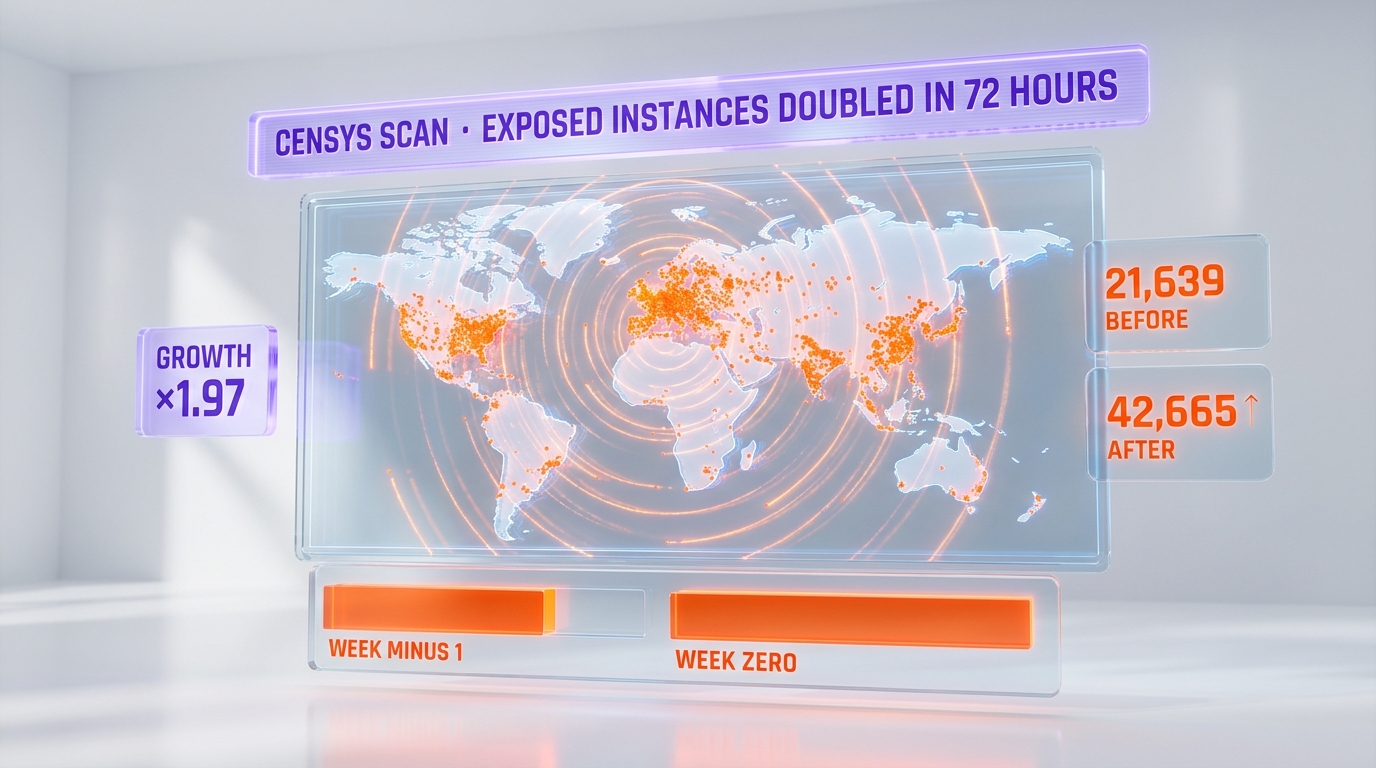
21,639 → 42,665: what the Censys doubling actually tells us
The number we are watching most carefully is the doubling of indexed instances in 72 hours. Before the CVE landed, Censys was tracking 21,639 internet-reachable OpenClaw gateways. By 72 hours after disclosure, the count sat at 42,665. The naive read is "the population doubled." That is not what happened.
The actual story is that Censys updated its scan signature once the unpatched OpenClaw fingerprint became public, and the new signature caught instances the previous signature was missing — mostly behind reverse proxies, non-default ports, and containerized deployments that the prior fingerprint did not match. The real population was always closer to the 42,665 number. The 21,639 was an undercount.
This matters because it is a recurring pattern in agent-runtime telemetry. Self-hosted agents proliferate through informal channels — docker-compose templates, one-line install scripts, internal tooling forks — and they do not announce themselves to asset inventory systems. The "we have 200 OpenClaw deployments" answer your CISO gets from the CMDB is almost certainly an undercount, and the gap between the CMDB number and the real number is where most of the unpatched 42,665 sit today.
For the same reason, the 42,665 number itself is a floor, not a ceiling. There are OpenClaw instances behind corporate firewalls that no external scanner will catch, and the WebSocket hijack chain works against them too as soon as one employee opens the wrong page on a corporate laptop. The internet-reachable count is the visible tip; the corporate-internal exposure is what we expect to drive the next 12 months of incident-response work.
93.4 percent authentication bypass: what the number measures
The 93.4 percent figure has been quoted everywhere, sometimes without the context that makes it meaningful. It is the share of reachable OpenClaw deployments in the affected version range that either (a) accepted the malicious gatewayUrl path without firing a user-confirmation prompt, or (b) auto-paired the attacker device because the connection appeared to originate from localhost. The remaining 6.6 percent had user prompts manually enabled, were running custom auth middleware, or were behind reverse proxies that stripped the malicious query parameters.
The 6.6 percent is the population that thought to harden the defaults. The 93.4 percent is the population that ran the project as documented. We are not pointing at user error here; we are pointing at a default that should have been the opposite. The right default for a service that listens on a port any browser tab can reach is "prompt before auto-pairing, always." The OpenClaw maintainers chose "auto-pair from localhost, no prompt." Both were defensible decisions in 2023. In 2026, with the deployed population we now know about, only one of them survives contact with reality.
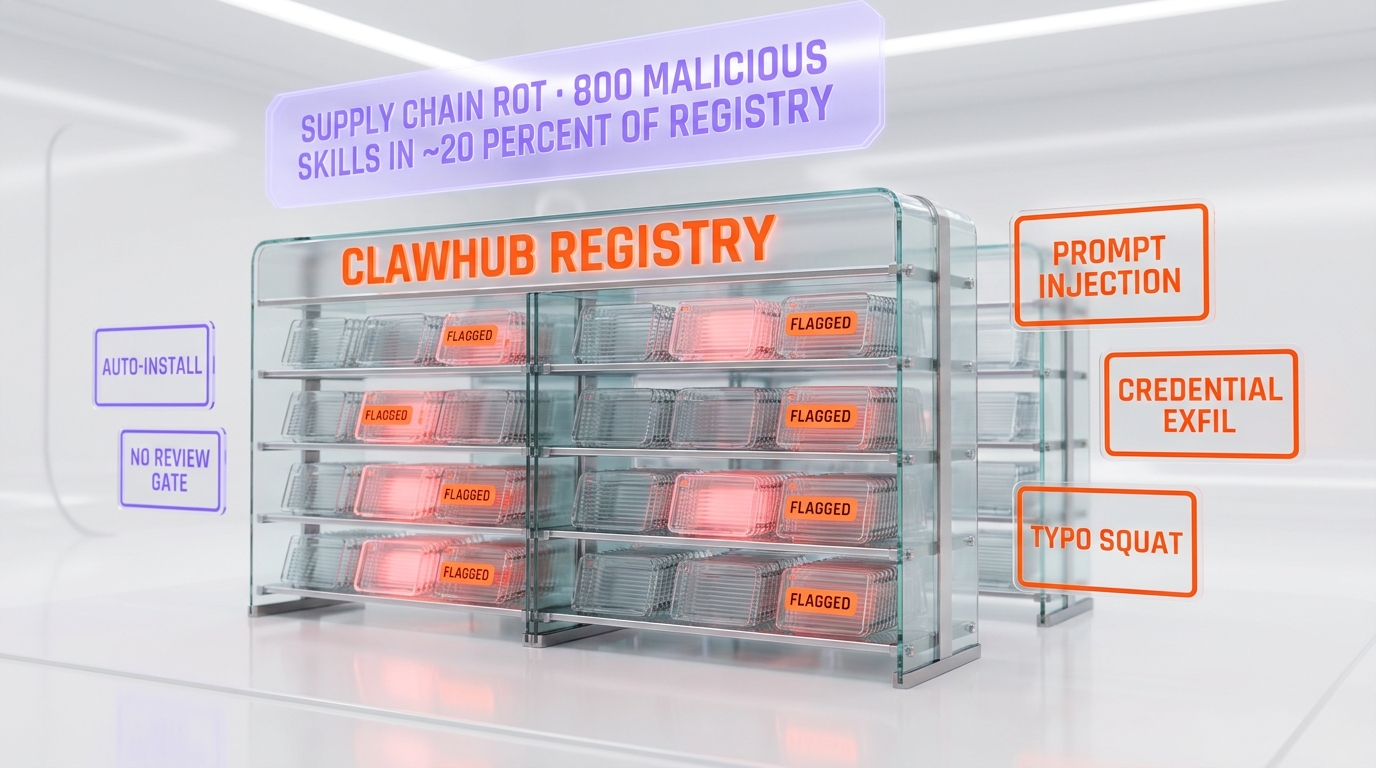
The 800 malicious skills problem in ClawHub
The CVE itself is one attack surface. The ClawHub skill registry is a second, and the two amplify each other in ways that need to be named clearly. Once an attacker has token-auth control of a target agent via the WebSocket chain, the obvious next step is to install a persistent malicious skill from ClawHub that survives the next agent restart. Defender community sweeps in the week after disclosure flagged roughly 800 skills out of a ~4,000-skill registry as showing one or more of the following signatures:
- Prompt injection payloads embedded in skill metadata that redirect the agent toward attacker-controlled URLs the next time the skill is invoked.
- Credential exfiltration logic wrapped in legitimate-looking functionality (a skill that "fetches your Slack messages" but also posts API keys to an attacker endpoint).
- Typosquat naming targeting common skill names (
github-searchvsgithub-searchervsgithub_search) where the squat package contains additional outbound calls. - Dependency confusion on package names that overlap with private internal skill repos.
20 percent of a registry being malicious or suspicious is not a normal supply chain number. For comparison, npm's persistent malicious package rate after years of automated scanning sits in the low fractions of a percent. The right frame is not "ClawHub is bad" but "no review gate existed between user-submitted skills and one-click install on a self-hosted agent that holds production credentials." The gate is what npm, PyPI, and the major package managers learned to install over a decade of supply-chain attacks. Skill registries are now learning the same lesson on a compressed timeline, and ClawHub got the first major bill.
For readers tracking the supply-chain attack pattern across ecosystems, the PyTorch Lightning Shai-Hulud malware supply chain attack earlier this year hit the same conceptual surface — trusted registry plus one-line install plus elevated downstream privileges — through a different ecosystem. CVE-2026-25253 is the agent-runtime variant of that story.
The 24-hour patch: what the OpenClaw team got right
The patch story is the unambiguous good news. Oasis Security disclosed privately on May 10, 2026. OpenClaw shipped v2026.1.29 on May 11, 2026 — inside the 24-hour window the disclosure terms allowed. The patch makes three changes:
- The
gatewayUrlquery string parameter no longer triggers an automatic outbound connection. A user-confirmation prompt fires for any non-loopback gateway, and the prompt cannot be auto-dismissed by JavaScript on the page. - The pairing endpoint now applies rate limiting to loopback connections, capped at a configurable per-minute threshold with default safe values.
- Session tokens are no longer auto-submitted in the WebSocket handshake; they require an explicit second-step authentication that cannot be triggered from cross-origin browser JS.
24 hours from private disclosure to a shipped patch on a project with this much surface area is a strong response. We say that without qualification. Patch velocity in the agent-runtime space has historically been measured in weeks, not days; OpenClaw moved at the upper end of what we have seen in 2026. What patch velocity does not fix is the deployment lag. We expect a long tail of unpatched 2026.1.28-or-earlier OpenClaw instances reachable from the public internet for the next 6 to 12 months, because that is how every previous mass-vulnerability patch curve has played out.

The agent-era security model is fragile — five structural failures CVE-2026-25253 exposes
This is where the analysis gets uncomfortable. We are going to lay out five structural problems with how agent runtimes are designed in 2026, all visible inside CVE-2026-25253, and all present in agent stacks that are not OpenClaw.
Failure 1 — Localhost is no longer a trust boundary
The implicit assumption baked into every self-hosted agent runtime we have looked at is that loopback connections are trusted because they originate from the same machine. That assumption was reasonable in 2010, when "same machine" meant "you, sitting at your keyboard, typing commands." It is not reasonable in 2026, when "same machine" includes any browser tab the user has open on any website. The trust boundary has moved up the stack, from "machine boundary" to "user-confirmation boundary," and agent runtimes have not finished the move.
Failure 2 — Skill registries replicate the npm 2014 problem
Skill registries are the package managers of the agent era, and they are recapitulating exactly the same supply-chain attack patterns that npm, PyPI, and RubyGems went through a decade ago — but compressed into months instead of years. No review gate. No mandatory signing. No dependency confusion protection by default. No typosquat detection. The mature package-manager ecosystem learned these lessons; the skill-registry ecosystem will, and the question is whether it does so before or after the next 800-malicious-package event.
Failure 3 — Agents hold production credentials by design
The pitch of a self-hosted agent runtime is "give it access to your tools and it will work for you." In practice, that means the agent holds API keys for Slack, GitHub, Jira, AWS, internal databases, and frequently more. When the agent is compromised, all of those access tokens are compromised. The blast radius of an agent-runtime CVE in 2026 is closer to "domain admin" than to "single endpoint compromise." This is not unique to OpenClaw; it is the model.
Failure 4 — Browser trust boundaries leak through agents
The malicious page never directly accesses the user's Slack workspace. It accesses the agent, and the agent accesses Slack. The user's same-origin policy did exactly what it was supposed to do — kept the malicious page out of Slack's cookies. What it could not stop was the agent acting as a confused deputy. Browser security has spent 25 years building the same-origin trust model. Agent runtimes broke it by sitting between the browser and the user's other accounts.
Failure 5 — Patch velocity is necessary but not sufficient
OpenClaw patched in 24 hours. That is genuinely excellent. It also did not help the operators who do not auto-update, do not subscribe to the security mailing list, do not read SecurityWeek, and will be running 2026.1.28 in production six months from now. Patch velocity solves the "informed operator" problem. It does not solve the "long-tail unpatched deployment" problem, and that population is where the actual exploitation will happen between now and end of 2026.
Where this sits in the 2025-2026 AI security incident arc
CVE-2026-25253 is the most visible AI-runtime CVE of 2026 so far, but it is not the only major incident in the arc. The pattern we are tracking is that 2025 incidents were mostly about misuse of frontier models — bad-faith prompts, jailbreaks, content-policy circumvention — while 2026 incidents are increasingly about the infrastructure layer underneath the models: agent runtimes, skill registries, deployment surfaces, supply chain.
For readers building a mental map: the Claude-assisted Mexico water utility hack documented by Dragos sits on the misuse-of-frontier-models axis — a threat actor using a capable model as offensive tooling against critical infrastructure. CVE-2026-25253 sits on the infrastructure-CVE axis — a self-hosted runtime being compromised independent of which model it is wrapping. The two will increasingly converge, and the worst incidents will be the ones that combine misuse of a frontier model with compromise of the runtime hosting it.
On the defensive side, Anthropic's Claude Security public beta announced April 30, 2026 represents one frontier lab's bet that AI itself is the only thing that scales fast enough to catch CVEs like this one before deployment. The bet is unproven but the timing is uncanny — Claude Security shipped 11 days before CVE-2026-25253 landed, and the exact patch class it is designed to catch is the auto-submit-without-prompt pattern that broke OpenClaw.
On the policy side, OpenAI's EU Cyber Action Plan launch and the GPT-5.5-cyber positioning against Anthropic Mythos earlier this month set up exactly the regulatory contest CVE-2026-25253 now has to play out inside. Brussels reads "first agent-era major CVE" differently than US incident-response, and the next round of Code of Practice guidance under the EU AI Act will reference this incident by name.
What defenders should do this week
The defender playbook for CVE-2026-25253 is short and unambiguous. We are listing it here because every other section of this piece is analysis, and we do not want the operational takeaway buried.
- Upgrade every reachable OpenClaw instance to 2026.1.29 or later. Includes containerized deployments, dev laptops, CI/CD runners, anything internal. The patch is non-breaking for documented use cases.
- Audit ClawHub installed skills against the community-published malicious-skill list (the Oasis Security disclosure thread is the primary reference). Remove anything flagged. Document what was installed and when.
- Block external traffic to OpenClaw default ports at the perimeter. Require VPN access for any remote pairing flow. If you are running OpenClaw on internet-facing infrastructure today, you are part of the long-tail population this CVE will keep paying out against for the next 6 months.
- Rotate every credential, API key, and session token the agent touched before the patch. Slack, GitHub, AWS, internal databases. Treat the rotation as you would after a confirmed credential breach, because for the 93.4 percent of instances the chain affected, you do not have evidence that it did not happen.
- Add detection for the WebSocket localhost pattern in your EDR. CrowdStrike, SentinelOne, and Microsoft Defender for Endpoint all pushed detection content within days. CrowdStrike coverage is the broadest; verify your tenant has the relevant signatures enabled.
- Audit other self-hosted agent runtimes in your environment for the same architectural pattern. If they listen on localhost, accept gateway URLs from query strings, and auto-pair without prompts, they have the same problem and probably do not have a patch yet.
Does Claude, Codex, or another major agent have the same problem?
This is the question we have been asked most this week, and the honest answer is "not in the same way, but the threat model is not zero." A breakdown of the major agent runtimes in the market and where they sit on the relevant surface:
- Anthropic Claude (desktop app, Claude Code, mobile): routes through authenticated Anthropic API, no open localhost WebSocket gateway in the documented surface. The closest analog is Claude Code's local MCP servers; those run scoped to the project directory and require explicit user invocation. Different threat model.
- OpenAI Codex CLI: similar pattern to Claude Code. Authenticated cloud API plus local invocation. No open WebSocket gateway.
- Browser-extension based agents: this is the surface we are watching most carefully. Extensions sit inside the browser's trust boundary already and route through the user's authenticated sessions. They have a structurally similar exposure to CVE-2026-25253, just expressed through a different transport (DOM events instead of WebSocket). We expect renewed security attention on this category in the next 90 days.
- Self-hosted Claude-API wrappers (LangChain, LlamaIndex, AutoGen agents): depends entirely on the wrapper. If the wrapper exposes a local HTTP or WebSocket gateway and accepts configuration from query strings, the same chain probably applies. We have not seen public CVEs in this category yet; we expect them.
- OpenClaw itself: patched and recovering. The maintainer response was strong, and we believe the project is in a better security posture today than it was two weeks ago.
What changes in the agent ecosystem after CVE-2026-25253
Three things shift, in our read, on a time horizon that is shorter than the next 12 months.
Skill registry review gates become the default. ClawHub will implement a mandatory review step, package signing, and typosquat protection before end of Q3 2026 — they have no choice. Other skill registries will follow. This is the npm 2018 moment for the agent ecosystem, and it will move quickly because the visible cost of not moving is now public.
Localhost stops being a trust boundary for new agent runtime designs. The next generation of agent runtimes will require user-confirmation prompts on any non-default gateway configuration, regardless of origin. Some of the existing runtimes will retrofit; some will not, and they will produce the next round of CVEs. We expect at least one more agent-runtime CVE at the CVE-2026-25253 magnitude before end of 2026.
Agent-runtime security becomes its own product category. Today, agent runtimes are sold on capability — what they can do, how many tools they integrate, how good the reasoning is. After CVE-2026-25253, security posture becomes a primary axis of differentiation. The vendors that get ahead of this — Anthropic with Claude Security, the EDR primes with agent-aware detection content — will price the gap. The vendors that do not will eat the next CVE.
The bottom line — and what would change our read
CVE-2026-25253 is, in our read, the agent-era's first scaled security crisis. Not the first agent CVE (there have been smaller ones), not the worst attack chain ever published (the technical primitives are routine), but the first one where the deployed-population number, the bypass rate, the registry contamination, and the policy attention all aligned at the same magnitude. The patch is shipped. The structural fragility is not, and that is what will determine whether the next 12 months produce a comparable CVE or whether the ecosystem matures faster than its attackers.
We will revise this read if (a) follow-on disclosures show the malicious-skill count was meaningfully inflated by false positives, (b) Censys data over the next 30 days shows the unpatched population dropping below 5,000 instances faster than precedent suggests, or (c) a second agent-runtime CVE of comparable magnitude lands and reveals a different structural failure than the five we have outlined. Anything else, and we expect the pattern we have described to hold.
Frequently asked questions about CVE-2026-25253
What is CVE-2026-25253 in one sentence?
CVE-2026-25253 is a high-severity (CVSS 8.8) one-click remote code execution flaw in OpenClaw before version 2026.1.29 that lets any malicious webpage hijack a self-hosted agent by tricking it into opening an attacker-controlled WebSocket and auto-submitting its own auth token.
How many OpenClaw instances were actually exposed on the public internet?
Censys went from indexing 21,639 internet-reachable OpenClaw gateways the week before disclosure to 42,665 once defenders started scanning for the unpatched signature, an effective doubling in roughly 72 hours. The doubling is mostly improved visibility, not new deployments, which means the real exposure was always closer to the higher number.
What does "93.4 percent authentication bypass" actually mean here?
Oasis Security and follow-on researchers measured that 93.4 percent of reachable OpenClaw deployments on the patched-or-unpatched version range either accepted the malicious gatewayUrl path without prompting the user, or auto-paired the attacker device because the connection appeared to originate from localhost. The remaining 6.6 percent had user prompts disabled or manual auth, which the chain still bypassed in some configurations.
What is the WebSocket hijack technical chain?
Step one: a malicious website embeds JavaScript that opens a WebSocket to ws://localhost on the OpenClaw default port. Step two: the page passes a gatewayUrl query string that points the agent at an attacker server. Step three: OpenClaw auto-connects and submits its token because no user-confirmation prompt fires on loopback. Step four: the attacker server is now the agent gateway and can issue shell commands, read files, and exfiltrate credentials.
What is the 800 malicious skills story in ClawHub?
Defender community sweeps after the CVE landed identified roughly 800 skills in the ClawHub registry showing signs of prompt injection payloads, credential exfiltration logic, or typosquat naming, against a registry of around 4,000 skills total. The 20 percent figure is the headline; the underlying issue is that no review gate existed between user-submitted skills and one-click install on a self-hosted agent.
Has the OpenClaw maintainer patched it yet?
Yes. OpenClaw shipped 2026.1.29 within 24 hours of receiving the Oasis Security disclosure. The patch closes the gatewayUrl auto-submit path, requires explicit user confirmation for non-loopback gateway changes, and adds rate limiting to the pairing endpoint. Anyone running 2026.1.28 or earlier remains exposed until they upgrade.
Is this the first agent-era security crisis or are we overstating it?
We read it as the first agent-era crisis at scale. Earlier 2025 agent-runtime CVEs existed but stayed in the low thousands of exposed instances and were patched before defender community attention organized. CVE-2026-25253 is the first time a single one-click chain affected a five-figure population of internet-reachable agent runtimes alongside a contaminated skill registry. That combination is the structural signature analysts will watch for in coming agent-ecosystem incidents.
Who else uses the OpenClaw codebase, since it is also called clawdbot and Moltbot?
The NVD entry lists OpenClaw, clawdbot, and Moltbot as the same affected codebase. clawdbot is the upstream Node.js runtime; Moltbot is a downstream packaging used by some hosting integrations. All three share the vulnerable gatewayUrl handler, so a CVE-2026-25253 patch advisory applies to all three names.
Does Claude, OpenAI Codex, or another major agent runtime have the same flaw?
Not as of writing. Anthropic Claude desktop and Claude Code, OpenAI Codex CLI, and the mainstream cloud agent runtimes route through authenticated APIs rather than open localhost WebSocket gateways. The closest comparable surface is browser-extension based agents, which we expect to receive renewed security attention now that the CVE-2026-25253 chain is public.
What should defenders do this week if their organization runs OpenClaw?
First, upgrade every reachable instance to 2026.1.29 or later. Second, audit ClawHub installed skills against the community-published malicious-skill list and remove anything flagged. Third, block external traffic to OpenClaw default ports at the perimeter and require VPN access for remote pairing. Fourth, rotate any credentials, API keys, or session tokens that touched the agent runtime before the patch.
Does CrowdStrike or another EDR vendor detect this attack chain?
CrowdStrike and SentinelOne both pushed detection content within days of the disclosure focused on the WebSocket localhost pattern, gatewayUrl path traversal, and post-exploit shell spawn signatures. Coverage is not perfect — the attack chain runs entirely in user-mode browser plus agent-runtime processes — so EDR alone should not be the primary control. Network controls and the OpenClaw patch are the higher-leverage fixes.
Is this a one-off bug or a structural problem with agent runtimes?
Structural in our read. The pattern that broke here — local agent listens on loopback, browser is treated as trusted because it is local, skills install with no review — is the default architecture in most self-hosted agent stacks today. CVE-2026-25253 is the first major surface where that pattern produced a five-figure exposure event. Without trust-boundary redesign across the agent ecosystem, we expect a comparable CVE in another runtime within the next two quarters.