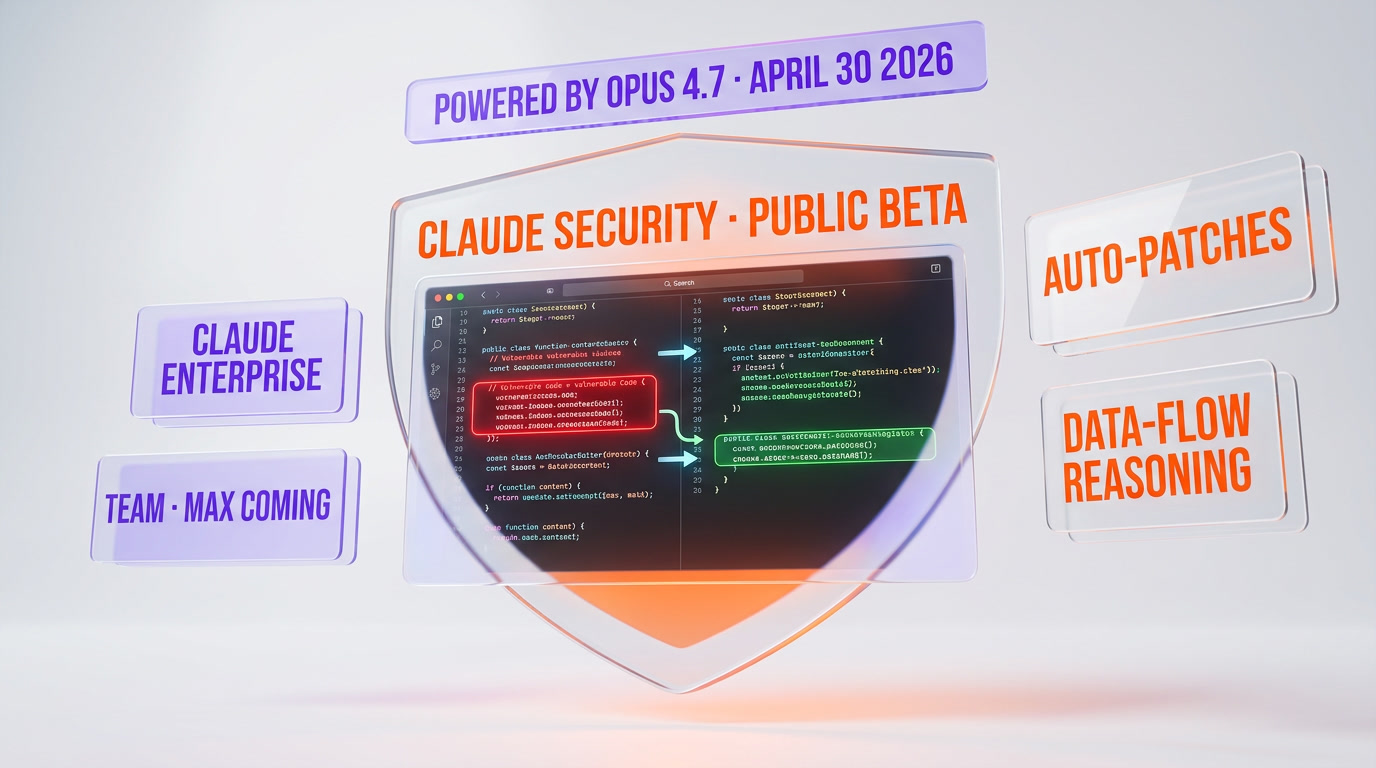
Anthropic launched Claude Security in public beta on April 30, 2026. The product is powered by Claude Opus 4.7 and ships with vulnerability scanning plus auto-generated patches for entire codebases. Access is open today only to Claude Enterprise customers; Anthropic has confirmed Team and Max tiers are coming soon. The release moves Anthropic into the same buyer conversation as Snyk, Sonatype, Veracode, Semgrep, and GitHub Advanced Security — and it is the fifth vertical Anthropic has attacked in the last 90 days.
TL;DR — what shipped on April 30, 2026
- Status: Public beta. Not GA. Available now from the Claude.ai sidebar or at claude.ai/security.
- Tier access: Claude Enterprise customers only on day one. Team and Max access "coming soon" per Anthropic — no firm date.
- Engine: Claude Opus 4.7. Same model that powers Claude Code; here it is wrapped in a security-purpose UI and a multi-stage validation pipeline.
- Detection method: Not pattern matching. Anthropic states Claude "traces data flows and examines how components interact across files and modules."
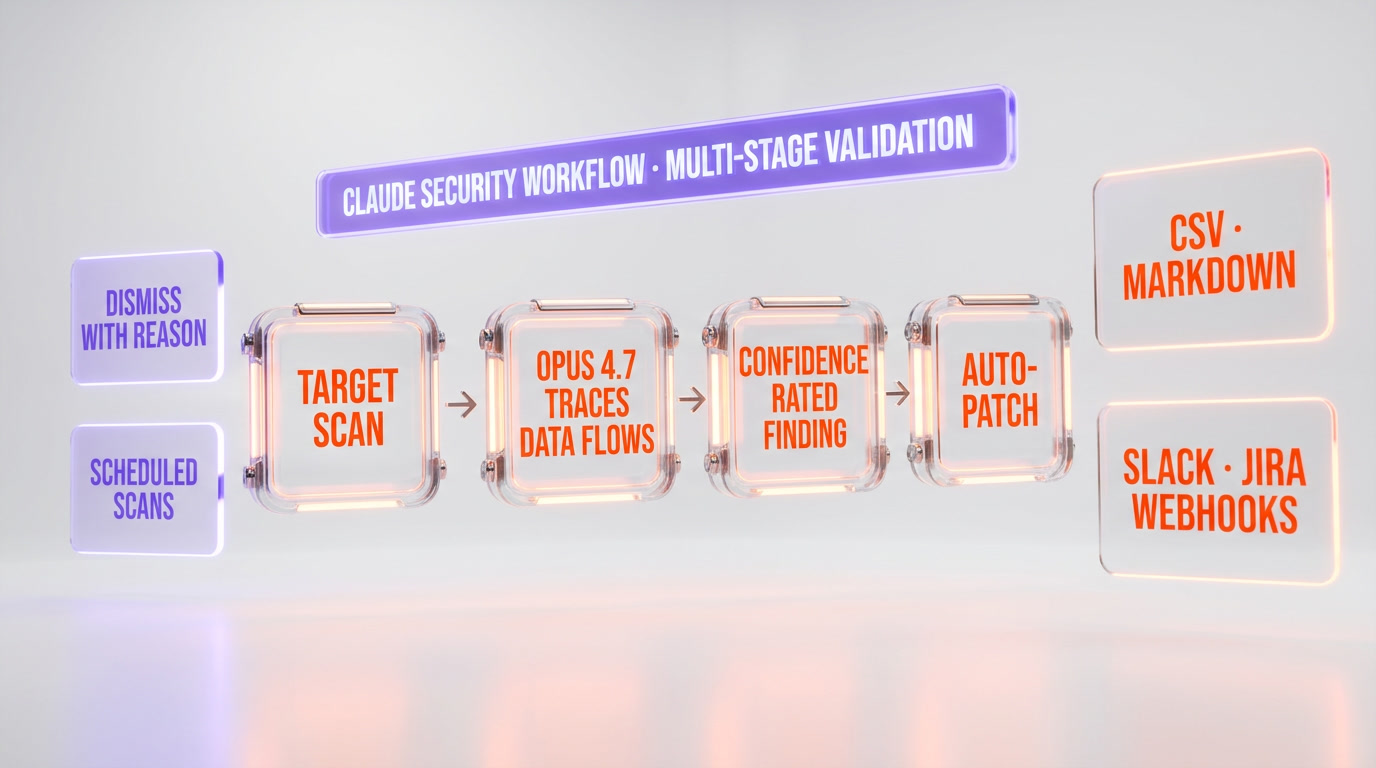
- Output: Severity assessment, reproduction guidance, confidence rating, and a generated patch for each finding.
- Workflow: Targeted directory scans, scheduled scans, dismiss-with-reason, CSV/Markdown export, Slack/Jira webhook integrations.
- Pre-launch testing: Anthropic tested the system with "hundreds of organizations" during a research preview, including Snowflake.
- Pricing: Not publicly disclosed. Bundled into Claude Enterprise on launch day.
What happened
On April 30, 2026 Anthropic published the Claude Security announcement page on its newsroom. The product entered public beta the same day for Claude Enterprise customers and started showing up in the Claude.ai sidebar shortly after. Coverage from Help Net Security, IT Pro, SiliconANGLE, Cybersecurity News, and Infosecurity Magazine landed across April 30 through May 4 as journalists got hands-on with the release.
Anthropic's framing is direct: Claude Security finds vulnerabilities in source code and writes the patches. Not a scanner that flags suspect lines for a human to triage — a system that produces the diff. Confidence ratings ride alongside every finding so engineering teams can decide whether to merge, review, or dismiss.
Two design choices stand out compared to existing security tooling. First, the analysis is reasoning-driven rather than rule-based: Claude reads the code the way a security researcher reads a code review, tracing how user input flows through functions, modules, and files until it reaches a sink. Second, the validation pipeline is multi-stage — the system attempts to reduce false positives before a human ever sees the queue, and it surfaces a confidence percentage with each result. Both decisions are aimed at the chronic noise problem that has plagued legacy SAST products for two decades.
Why it matters: Anthropic just walked into the security software vertical
Application security is not a small market. The category that includes Snyk, Sonatype, Veracode, Semgrep, Checkmarx, and GitHub Advanced Security is regularly sized between $7 billion and $11 billion in annual recurring revenue depending on whose analyst report you trust, with double-digit annual growth and tight enterprise renewal economics. Snyk alone closed its last public funding round in December 2022 at a $7.4 billion valuation after peaking at $8.5 billion in September 2021. Sonatype is private and processes more than 600 billion software component requests per year. Veracode was taken private by TA Associates in 2022 in a deal that valued it around $2.5 billion. GitHub Advanced Security is a paid add-on to GitHub Enterprise priced per committer.
That is the buyer pool Anthropic just walked into. And the angle of attack is not "buy our scanner, it has more rules." The angle is "the scanner reads your code like a senior security engineer would, then writes the fix." If Claude Security delivers on that promise even partially, the procurement conversation in CISO offices changes shape immediately.
The pre-existing CISO playbook is well-rehearsed: license a SAST tool from Snyk, Veracode, or Checkmarx; license SCA from Sonatype; bolt on Semgrep for custom rule packs; integrate everything into the GitHub or GitLab pipeline; staff a dedicated AppSec team to triage the resulting noise. Every one of those line items is now a candidate for partial or full displacement by a single vendor that already sits inside the Enterprise contract — Anthropic.
How it actually works: the data-flow reasoning angle
Traditional SAST tools work primarily by pattern matching. They have rules that say things like "if you see request.params.id being concatenated into a SQL string, flag it." Pattern matching catches obvious cases and misses anything that requires understanding the rest of the codebase. The accuracy ceiling is real and well-studied — most of the best legacy scanners report false-positive rates in the 30 to 70 percent range on enterprise Java and Python codebases, which is why every AppSec team has a triage backlog.
Claude Security takes a different route. Anthropic describes the analysis as Claude "tracing data flows and examining how components interact across files and modules." In practical terms, Opus 4.7 reads the source files, builds an internal model of how user-controllable input enters the application, follows that input across function boundaries and module boundaries, and reasons about whether each downstream usage constitutes a real vulnerability. The model can also reason about the patch — given the bug it just identified, what is the minimal code change that closes the issue without breaking the surrounding logic?
This is an approach legacy scanners cannot easily replicate. They are built on AST traversal, taint analysis, and rule libraries — none of which scale gracefully to "explain what this 40,000-line service actually does and where the unauthenticated paths are." A frontier reasoning model can. Whether it can do so reliably enough to displace incumbent contracts is the open question, and the next twelve months of customer benchmarks will answer it.
How Claude Security compares to the incumbents
Below is the buyer-side comparison as of May 2026. Pricing for Claude Security is bundled into Enterprise — Anthropic has not separated the line item publicly — so the column is best-effort.
| Vendor | Detection method | Auto-patches | Pricing model | Best known for |
|---|---|---|---|---|
| Anthropic Claude Security | Reasoning, data-flow tracing across modules | Yes — patch instructions ship with each finding | Bundled into Claude Enterprise | Reasoning over codebases, low-noise findings |
| Snyk | Hybrid AST + ML, large rule library | Snyk DeepCode AI fix suggestions | $25 per developer per month entry, enterprise quote | Developer-first DX, IDE integrations |
| Sonatype | SCA — open source component intelligence | Pull-request remediation suggestions | Quote-based | Software supply chain, OSS advisory feed |
| Veracode | SAST + DAST + SCA, rule-based | Veracode Fix (AI-suggested patches) | Quote-based | Compliance-grade enterprise SAST |
| Semgrep | Lightweight rule engine, customizable | Suggested fixes, mostly rule-driven | Free tier + paid plans from $40 per seat per month | Custom rules, fast scans, OSS-friendly |
| GitHub Advanced Security | CodeQL queries + secret scanning | Copilot Autofix (AI patch generation) | $49 per active committer per month | Native GitHub integration, public-repo coverage |
The comparison highlights something we have been watching for two years: every legacy AppSec vendor now ships an AI-patch feature, but none of them ship the patch as the headline. Snyk DeepCode AI, Veracode Fix, and GitHub Copilot Autofix are bolt-ons. Claude Security inverts the ratio — patch generation is the product, not the side feature.
The Snowflake signal and the buyer journey
Anthropic surfaced one named design partner during the public beta launch: Snowflake. A Snowflake staff product security engineer told reporters Claude Security "surfaced novel, high-quality findings" — a quote that has been used in the launch coverage by IT Pro and others. That is a meaningful endorsement. Snowflake operates one of the most security-sensitive cloud platforms in the world; if Claude Security clears the bar at Snowflake, it clears the bar at most enterprise CISO procurement boards.
For an enterprise CISO evaluating Claude Security in May 2026, the buyer journey looks something like this:
- Already on Claude Enterprise? Turn on Claude Security in beta this week. Pilot it on one repo in parallel to your existing SAST. Compare findings.
- Not on Claude Enterprise but on Snyk/Veracode/Sonatype? The contract is renewing in 6-18 months. The CFO conversation about consolidating onto Anthropic just got concrete.
- Multi-vendor stack with a high noise budget? Track false-positive rate during pilot. Multi-stage validation plus confidence ratings is the test that matters here.
- Compliance-driven (PCI, SOC 2, FedRAMP)? Wait for GA and a SOC 2 Type II report on Claude Security specifically. Beta status is a blocker for compliance-anchored procurement.
The fourth point is real. Public beta means change management risk. Compliance-led security buyers (banks, healthcare, defense suppliers) will not move production AppSec onto a beta product no matter how strong the early signal is. That gives the incumbents a 6-12 month moat at the high-compliance end of the market — but not at the mid-market or in cloud-native shops.

Anthropic's vertical strategy: five attacks in 90 days
Claude Security is not an isolated launch. It is the latest move in a clearly visible Anthropic vertical strategy that has accelerated since February 2026. We have covered each piece of the pattern already, and Claude Security clicks neatly into the picture:
- Biology — April 4, 2026. Anthropic acquired Coefficient Bio for $400 million to enter AI drug discovery.
- Finance — early May 2026. The Anthropic + Goldman Sachs + Blackstone $1.5B JV launched, plus 10 finance-vertical Claude agents went live for Citadel, BNY, and Carlyle.
- APAC distribution — late April 2026. The Anthropic + NEC deal announced Japan's largest AI-native engineering team — 30,000 NEC employees on Claude.
- Consulting — May 7, 2026. EPAM agreed to certify 10,000 architects on Claude in a structured partnership.
- Security — April 30, 2026. Claude Security public beta, the subject of this article.
The pattern reads as a deliberate "every vertical, every month" land-grab. Each vertical is an existing software market with an obvious incumbent set: drug discovery (BenevolentAI, Recursion, Insilico Medicine), finance copilots (BloombergGPT, FactSet, Refinitiv Workspace), Japanese systems integration (Fujitsu, Hitachi, NTT Data), management consulting (Accenture, Deloitte, McKinsey), and now AppSec (Snyk, Sonatype, Veracode, Semgrep, GitHub Advanced Security). Anthropic is converting one big horizontal product — Claude — into a vertical-by-vertical wedge that displaces an entrenched category leader at each step.
This pattern matters for any enterprise contract being renewed in 2026. The base rate that "the incumbent SaaS in your category will compete with a Claude-powered alternative within 12 months" has gone from speculative to roughly 100% in the categories Anthropic has visibly entered.
What's missing from the launch
Five things Anthropic has not disclosed publicly as of May 9, 2026:
- Pricing. Bundled into Enterprise, no separate per-seat or per-repo line item published.
- Vulnerability classes covered. Anthropic says "vulnerabilities" generically. No public list of OWASP Top 10 coverage or CWE class breakdown.
- Language and framework support. The launch posts confirm scanning across "files and modules" but not which languages are first-class.
- Throughput limits. No published numbers for max codebase size, scan duration on a 1M-line repo, or per-organization concurrency caps.
- Compliance certifications. No SOC 2 Type II report on Claude Security specifically as of the beta launch.
For procurement-led CISOs, those gaps are the real blockers. Expect Anthropic to fill them in the next 60-90 days as the product moves from public beta toward GA and as the Team and Max tier rollout starts. Once the missing data is on the table, the displacement conversation against incumbents stops being abstract.
What it means for developers using Claude Code today
Claude Code subscribers ask the obvious follow-up question: does Claude Security show up in my CLI? Not yet. Claude Security is a browser-first product on launch — it lives at claude.ai/security and inside the Claude.ai sidebar. There is no documented integration with Claude Code as of the public beta launch.
That said, the same Opus 4.7 model is doing the work in both products. If you have been asking Claude Code "scan this file for vulnerabilities" inside your terminal, you are exercising approximately the same reasoning capability — just without the multi-stage validation pipeline, the confidence rating, the dismiss-with-reason workflow, or the export to Slack/Jira. We expect Anthropic to either ship a "claude security" subcommand inside Claude Code or to merge the workflows in some other way once the dedicated product matures.
For our editorial workflow at ThePlanetTools, we have been running Claude Code on a daily basis since the Opus 4.7 launch in April, and the doubled rate limits from the SpaceX Colossus 1 deal have made longer reasoning chains practical. Claude Security is the same reasoning chain pointed at a focused problem domain. The capability is real; the productization is the new piece.
The competitive risk for Snyk, Sonatype, Veracode, Semgrep
Each incumbent faces a slightly different exposure:
- Snyk. Highest exposure. Snyk's developer-first positioning and IDE-led DX are exactly what a Claude-powered scanner can replicate at enterprise scale. The unanswered question for Snyk's IPO timeline is whether their AI features can keep parity with Anthropic's roadmap velocity.
- Sonatype. More insulated short-term. Software composition analysis (SCA) is an OSS-advisory data play, not a code-reasoning play. But Anthropic has the infrastructure to ship SCA next, and Sonatype's moat is built on data freshness more than on detection sophistication.
- Veracode. Compliance-bound enterprise customers are stickier. The TA Associates take-private gives Veracode runway. Risk concentrated in cloud-native customer segments where compliance is lighter.
- Semgrep. Strong OSS community and custom-rule story. The GitOps niche is defensible. Direct head-to-head most likely on price-sensitive mid-market accounts.
- GitHub Advanced Security. Microsoft-owned, distribution-led, deep GitHub integration. The defensive moat is "you're already on GitHub Enterprise." Risk only if Anthropic ships native GitHub integration via the Anthropic Connectors.
None of these vendors disappear in 2026. But every one of them just got a new line in their next analyst-day deck explaining how they plan to defend against Anthropic. The honest version of that explanation involves either a technology partnership with a frontier-model lab (most likely OpenAI for the Snyk-class vendors) or a years-long bet on proprietary data moats. Neither is a quick answer.
What we will be watching over the next 90 days
- GA timeline. When does Claude Security exit public beta? An RC milestone with SOC 2 Type II in hand is when compliance-led buyers can start signing.
- Team and Max access. "Coming soon" is vague. The mid-market opens up the moment Team-tier customers can subscribe.
- Pricing surface. A separate Claude Security SKU with per-repo or per-developer pricing is the signal Anthropic is going horizontal in security rather than keeping it inside the Enterprise bundle.
- Language coverage announcements. First-class support announcements for Java, Go, Rust, and TypeScript will signal the codebases Anthropic is targeting first.
- Snyk and Veracode's response. Major announcements at RSAC 2026 (already past) and Black Hat 2026 (August) will define how the incumbents counter-position.
- Compliance certifications. FedRAMP and SOC 2 Type II on Claude Security specifically. Without these, US federal and regulated-industry customers cannot move.
Our take
Claude Security is the most strategically clear product Anthropic has shipped in 2026. Coding tools are the obvious place a frontier reasoning model excels, and security is the highest-margin, most-renewable slice of the coding-tool market. Anthropic going there directly — with a public beta priced into the Enterprise bundle on day one — is the kind of move that reorganizes the buyer's office in the medium term.
The honest caveat is that public beta status, missing pricing transparency, missing language-support disclosure, and missing compliance certifications are real friction. We expect these to disappear in the next 60-90 days. We do not expect Snyk, Veracode, or Sonatype to disappear — but the question of which AppSec line items survive a 2026-2028 enterprise renewal cycle just got materially harder for them to answer.
For an enterprise security buyer reading this in May 2026, the action item is small but real: if you are on Claude Enterprise, run a Claude Security pilot on a non-critical repo this week and benchmark the findings against your current SAST. The data point will inform every renewal you sign for the next two years. We have been testing Claude Code daily and the underlying reasoning capability of Opus 4.7 is real — security is the natural next domain for it. The compute story behind the product is documented in our coverage of Anthropic's 10-gigawatt compute empire, and the broader Anthropic vertical strategy threads through everything from the Mythos Preview reveal to the April Claude Code postmortem.
One launch a month, one vertical at a time. Snyk just got the call.
Frequently asked questions
Frequently Asked Questions
What is Anthropic Claude Security and when did it launch?
Claude Security is an AI-powered code vulnerability scanning and auto-patching product from Anthropic. It launched in public beta on April 30, 2026, powered by the Claude Opus 4.7 model. It is currently available only to Claude Enterprise customers, with Team and Max tier access "coming soon" per Anthropic. Access is via the Claude.ai sidebar or claude.ai/security — no API integration is required for the beta.
How is Claude Security different from Snyk, Sonatype, or Veracode?
Traditional scanners like Snyk, Sonatype, and Veracode rely primarily on pattern-matching, AST traversal, and rule libraries. Claude Security uses Claude Opus 4.7 to trace data flows and examine how components interact across files and modules — closer to how a human security researcher reasons about a codebase. Anthropic also bundles auto-generated patches with each finding rather than offering them as a side feature, which is the opposite ratio from the AI-fix add-ons currently shipped by Snyk DeepCode AI, Veracode Fix, and GitHub Copilot Autofix.
How much does Claude Security cost?
Anthropic has not disclosed standalone pricing for Claude Security as of the public beta launch. Access is bundled into the Claude Enterprise subscription on day one. Team and Max pricing has not been published — Anthropic only states those tiers are "coming soon." A separate per-seat or per-repo SKU may emerge as the product moves toward GA but has not been announced.
Can I use Claude Security if I am not on Claude Enterprise?
Not yet. Public beta access on April 30, 2026 was limited to Claude Enterprise customers. Anthropic has stated that Claude Team and Claude Max customers will get access "coming soon" without committing to a date. Free Claude users and Pro users have no announced path to Claude Security as of May 2026.
What features does Claude Security include?
The public beta ships with: targeted directory-level scanning, scheduled scans, dismiss-with-documented-reasons for findings, multi-stage validation to reduce false positives, confidence ratings on each finding, severity assessment, reproduction guidance, generated patch instructions, CSV and Markdown export, and webhook integrations with Slack and Jira. The product is accessible through the Claude.ai sidebar or directly at claude.ai/security.
Does Claude Security integrate with GitHub or GitLab?
The launch announcement does not list GitHub or GitLab as native integrations on day one. Output flows out of Claude Security via CSV, Markdown, and webhook integrations to Slack and Jira. Claude Security is browser-first via claude.ai/security in the public beta. We expect deeper Git platform integrations to ship before GA, but Anthropic has not committed publicly.
Which programming languages does Claude Security support?
Anthropic has not published an explicit list of supported languages with the public beta launch. The product description references scanning "across files and modules" without committing to a first-class language list. Given that Opus 4.7 powers Claude Code with broad language coverage, expect Java, Python, JavaScript/TypeScript, Go, Rust, and the major web frameworks to perform well in practice. Verifying coverage for less common languages requires hands-on testing.
Is Claude Security safe to use on production code?
Public beta status means change management risk. Anthropic ran a closed research preview with hundreds of organizations including Snowflake, whose product security engineer publicly stated Claude Security surfaced "novel, high-quality findings." But there is no SOC 2 Type II report covering Claude Security specifically as of May 2026, no FedRAMP authorization, and no published breakdown of false-positive rates by language or vulnerability class. Compliance-anchored buyers should run pilots, not production rollouts, until GA.
Does Claude Security replace GitHub Advanced Security?
Functionally, there is significant overlap — both products surface code vulnerabilities, and both ship AI-generated patches (GitHub via Copilot Autofix). GitHub Advanced Security is priced at $49 per active committer per month and is deeply native to the GitHub platform. Claude Security is bundled into Claude Enterprise. Replacement is plausible for cloud-native shops not anchored to GitHub-native compliance workflows; defensible for GitHub Advanced Security wherever the buyer values the GitHub-native integration depth and Microsoft contractual relationship more than Anthropic's reasoning advantage.
Why is Anthropic moving into security software?
Claude Security is the fifth vertical Anthropic has visibly entered in 90 days, alongside biology (Coefficient Bio acquisition for $400M), finance (Goldman Sachs and Blackstone $1.5B JV plus 10 finance agents), APAC distribution (NEC partnership with 30,000 employees), and consulting (EPAM 10,000 architect certification). The strategy is to convert Claude from a horizontal product into a series of vertical wedges that displace incumbent SaaS leaders at each step. Application security is high-margin, high-renewal, and a natural fit for a frontier reasoning model — which makes it an obvious target.
What is the biggest risk for Snyk after this launch?
Snyk's developer-first positioning and IDE-led DX are precisely what a Claude-powered alternative can replicate at enterprise scale. Snyk's most recent public valuation was $7.4 billion in December 2022, down from $8.5 billion in September 2021, with an IPO timeline that has been moving. Anthropic's roadmap velocity in security is the material risk to that timeline. Snyk's defense plays are: deeper IDE and developer-DX moat, faster Snyk DeepCode AI iteration, and potentially a frontier-model partnership of its own (most likely with OpenAI given Anthropic's competitive overlap).
When will Claude Security be generally available (GA)?
Anthropic has not committed to a GA date as of May 2026. The product launched in public beta on April 30, 2026. Typical Anthropic release cadence has moved features from public beta to GA in 60-180 days when telemetry supports it. SOC 2 Type II certification timelines tend to gate compliance-led GA announcements — those reports take six months to compile against a fully-implemented control set, so a Q3 or Q4 2026 GA window is the realistic earliest outlook for compliance-anchored buyers.