On May 11, 2026, OpenAI President Greg Brockman announced Daybreak, an umbrella global cybersecurity initiative powered by GPT-5.5 with Trusted Access for Cyber and a new Codex Security agent, alongside 20+ partners including Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Akamai, Snyk, Trail of Bits, and SpecterOps. Daybreak is the global play. The OpenAI EU Cyber Action Plan we covered yesterday was the regional overlay. Read together with Anthropic Glasswing — the closed four-hyperscaler coalition with Apple, Microsoft, Google, and Amazon — and Mythos preview, the May 11 announcement is the clearest formal split yet in how the two leading frontier labs intend to ship cyber defense. OpenAI is betting on coalition breadth. Anthropic is betting on coalition selectivity. Both bets are coherent. Only one of them can be right on the timeline that matters.
The announcement — Daybreak launches May 11, 2026
According to OpenAI's announcement and reporting from Decrypt, Engadget, MacRumors, and Yahoo Finance, Greg Brockman announced Daybreak on X on May 11, 2026, framing it as OpenAI's global cybersecurity initiative to help defenders identify vulnerabilities, validate fixes, and secure software faster using AI. The launch is built on the GPT-5.4-Cyber rollout from April 2026, which OpenAI says has already been used to fix more than 3,000 vulnerabilities since release. Daybreak extends that foundation with two new components — GPT-5.5 with Trusted Access for Cyber, and Codex Security, an agentic security tool built on Codex with autonomous threat modeling and vulnerability detection.
The initiative ships with what OpenAI characterizes as a partner list of 20+ companies spanning the global cyber defense stack. Per Engadget's reporting, the named partners include Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, and Akamai as headline collaborators. The expanded list, surfaced through complementary coverage and OpenAI's own publications, adds Zscaler, Fortinet, Intel, Qualys, Rapid7, Tenable, Trail of Bits, SpecterOps, SentinelOne, Okta, Netskope, Snyk, Gen Digital, Semgrep, and Socket. That partner roster is the operational engine of the launch. Daybreak without the vendor integrations is a press release. Daybreak with the vendor stack is a market position.
Key facts (per OpenAI announcement, Greg Brockman X post, Decrypt, Engadget, MacRumors, Yahoo Finance — May 11, 2026):
- Announcement date: May 11, 2026
- Announcer: Greg Brockman, OpenAI President (X post)
- Core tech: GPT-5.5 with Trusted Access for Cyber + Codex Security agent
- Foundation: GPT-5.4-Cyber (April 2026), reported by OpenAI to have fixed 3,000+ vulnerabilities
- Partner count: 20+ companies across global cyber defense stack
- Headline partners (per Engadget): Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Akamai
- Use cases: Secure code review, vulnerability triage, malware analysis, detection engineering, patch validation
- Codex Security capabilities: Threat model generation, vulnerability validation, autonomous detection of higher-risk issues
- Scope: Global umbrella initiative (the EU Cyber Action Plan, May 11, is the European overlay)
- Strategic context: Direct response to Anthropic Glasswing (Apple, Microsoft, Google, Amazon) and Mythos
The Daybreak architecture — three layers stacked on GPT-5.4-Cyber
Reading the announcement and partner statements, Daybreak organizes as three operational layers built on the April 2026 GPT-5.4-Cyber foundation. None of the layers are revolutionary in isolation. The combination is the bet.
Layer one — GPT-5.4-Cyber as the proven base. OpenAI's public framing says GPT-5.4-Cyber has been used to fix more than 3,000 vulnerabilities since its April rollout. That number is OpenAI's, not independently audited, and the company has not yet published a per-customer breakdown or a CVE-level enumeration. Read with appropriate skepticism, the 3,000 figure is still material. It is the first publicly claimed scale benchmark for AI-assisted vulnerability remediation from a frontier lab. The number gives Daybreak a credibility anchor that pure capability claims would not.
Layer two — GPT-5.5 with Trusted Access for Cyber. This is the access channel layered on top of the broader GPT-5.5 release. Per the OpenAI framing reported by Engadget, GPT-5.5 with Trusted Access for Cyber handles secure code review, vulnerability triage, malware analysis, detection engineering, and patch validation. The Trusted Access program is the same gating model used for the EU Cyber Action Plan and the broader GPT-5.5-Cyber rollout from May 7 — vetted application, security attestation, and a contractual usage perimeter. Daybreak does not loosen the gate. It puts the gate inside a larger coalition frame.
Layer three — Codex Security agent. This is the new primitive. Codex Security is built on Codex, OpenAI's agentic coding system, and adds two cyber-specific capabilities. First, it can generate a threat model from an organization's codebase automatically. Second, it can validate likely vulnerabilities and triage the higher-risk findings without a human running each prompt. Per Engadget's reporting of an OpenAI demonstration, Codex Security was tasked to scan a codebase, validate the highest-risk findings, and fix them — the full inner loop of defensive code maintenance compressed into an agentic workflow. If that demo holds at production scale, the implication is significant. Threat modeling is one of the most under-staffed disciplines in corporate security. Automating the first 80 percent of it changes the economics for thousands of mid-market security teams that have never had a dedicated threat modeler.

The partner roster — and why Snyk is the most interesting name on it
The Daybreak partner list reads, by category, as a methodical sweep of the cyber defense market. Network and edge infrastructure brings Cloudflare and Akamai. Enterprise networking and endpoint brings Cisco and Palo Alto Networks. EDR and XDR brings CrowdStrike and SentinelOne. Identity brings Okta and Netskope. Vulnerability management brings Qualys, Rapid7, and Tenable. Hyperscaler-adjacent infrastructure brings Oracle and Intel. Application security and software composition brings Snyk, Semgrep, and Socket. Specialized cyber consulting brings Trail of Bits and SpecterOps. Consumer and enterprise hybrid brings Gen Digital and Fortinet. Zero trust networking brings Zscaler.
The category that matters most is not the headline names. It is Snyk. We covered Anthropic Claude Security's May 2026 public beta launch as a direct competitive threat to Snyk's vulnerability scanning moat. Claude Security, also released in early May, positioned Anthropic to enter the same code security workflow Snyk has dominated for the better part of a decade. The market read at the time was that Snyk would be forced to either build a defensible AI strategy of its own or be squeezed between Anthropic's frontier model on one side and the existing SAST incumbents on the other.
One week later, Snyk is on the Daybreak partner list. The company is hedging both sides of the frontier AI cyber race. Anthropic's Claude Security threatens Snyk's product line. OpenAI's Daybreak invites Snyk into the coalition. From Snyk's vantage point the strategy is rational. Riding both labs preserves optionality. From the lab vantage point the same fact is more revealing. OpenAI was willing to put Snyk on the Daybreak marquee even with Anthropic Claude Security in the field. Anthropic, by contrast, chose to compete with Snyk directly through Claude Security rather than partner with it. The two choices reveal the two coalition philosophies in one data point. OpenAI builds broad. Anthropic builds narrow.
Strategic positioning — Daybreak as the direct response to Glasswing and Mythos
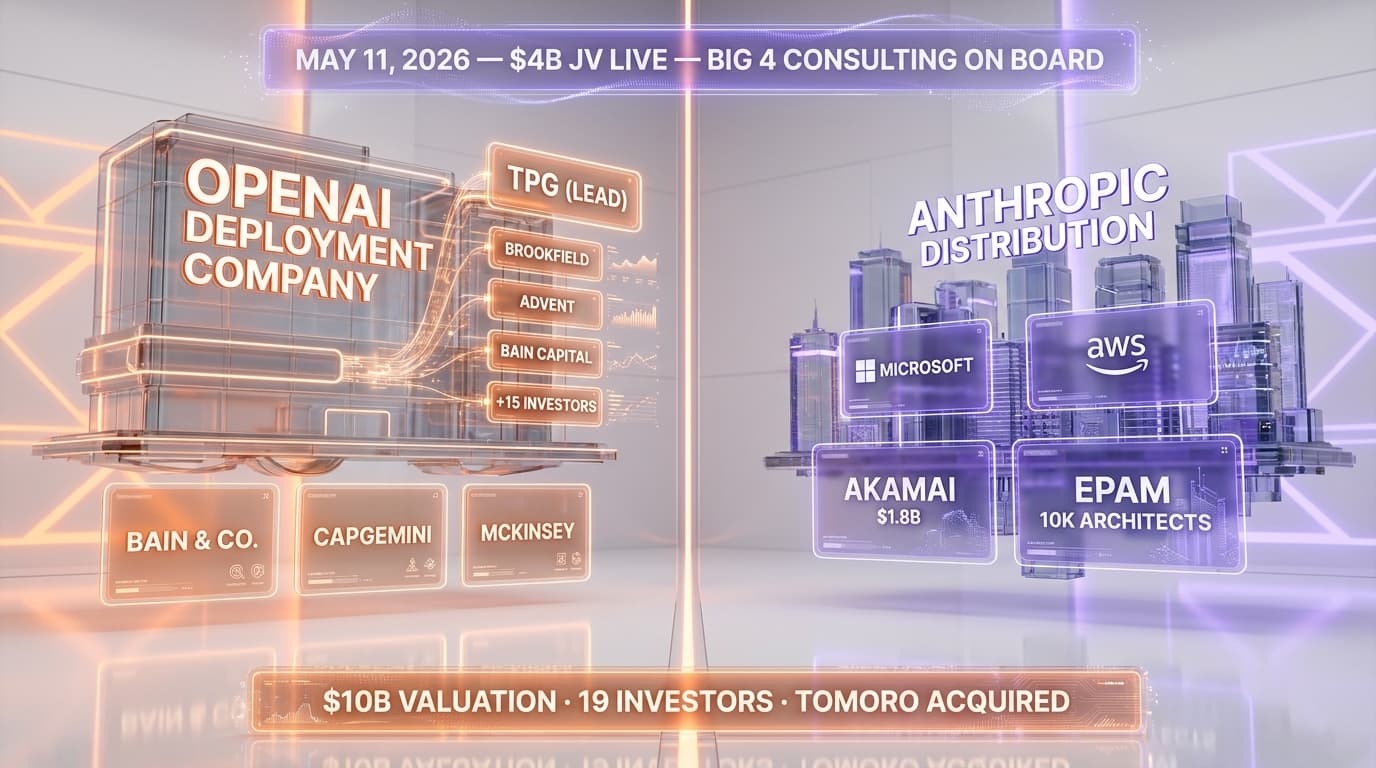
The strategic frame around Daybreak is impossible to read in isolation from the Anthropic Glasswing and Mythos cluster. Glasswing, Anthropic's enterprise security coalition, anchors on four hyperscalers — Apple, Microsoft, Google, and Amazon. Mythos preview, the more powerful sibling to Opus 4.7, ships in limited access with Trusted Access gating that has been more restrictive than OpenAI's parallel program. Together, Glasswing and Mythos define Anthropic's bet — small coalition, high-capability model, tight controls, safety-first framing.
Daybreak is the deliberate opposite vector on every axis. Coalition size — 20+ partners versus four. Coalition composition — full cyber defense stack versus hyperscaler quartet. Access model — Trusted Access for Cyber with vendor partners and active integrations versus narrow vetted-partner gating. Model deployment posture — visible production use cases (5 named workflows, demonstrated agent on stage) versus a more restrained "we are scoping access carefully" posture. The framing is not subtle. Daybreak is OpenAI's argument that the right way to ship frontier cyber AI is breadth-first, with the safety controls embedded in the partner contracts and account-level security rather than in the size of the access ring.
Both labs can support that argument with public data points. Daybreak partners include Trail of Bits and SpecterOps — two of the most respected adversary-emulation and offensive security firms in the world. If the access controls were too loose, those firms would not be lending their reputational capital to the launch. On the Anthropic side, the lab can point to the Mythos Discord breach on day one — where unauthorized Mercor contractor credentials surfaced inside an internal Anthropic Discord channel — as evidence that even tightly controlled access circles can leak. The Glasswing and Mythos posture is not paranoia. It is a response to documented incident data.

Daybreak vs Glasswing — the open coalition versus closed elite split
The cleanest frame for the May 11 split is open coalition versus closed elite. Daybreak is the open coalition. Glasswing is the closed elite. The two coalitions are not competing for the same partner pool. They are competing for the right structural frame.
The open coalition argument runs as follows. Cyber defense is not a closed problem. It scales by the number of integrations into existing operational defense workflows. The more partners shipping production integrations on a frontier defensive AI primitive, the faster the median defender on Earth gets the lift. The 20+ Daybreak partners are not all marquee names. Some of them — Socket, Semgrep, Gen Digital — are mid-tier or category specialists. That is the point. Coverage is the strategy. The breadth is the moat.
The closed elite argument runs the other direction. Frontier defensive AI is a dual-use capability. The same model that finds vulnerabilities in your codebase can find vulnerabilities in your adversary's codebase. The bigger the access ring, the wider the attack surface for misuse. Apple, Microsoft, Google, and Amazon, in the Glasswing frame, are not chosen because they need Mythos more than CrowdStrike does. They are chosen because they have the security maturity, the contractual depth, and the operational discipline to handle a model at the Mythos capability threshold without leaks compounding. Selection is the moat. Restraint is the strategy.
Both arguments are coherent. The empirical question is which one closes the offense-defense gap faster on the timelines that matter. If the Dragos report on the Mexico water utility Claude attack — 17,000 lines of malware, 195 million records compromised — represents the median case rather than the tail, the answer is whichever coalition gets defensive capability into production faster. If that same incident represents the leading edge of a tail risk that compounds with capability lift, the answer is whichever coalition prevents the next leak. The data does not yet decide between the two readings.
Codex Security — the agent layer that changes the procurement math
The Codex Security agent is the single product within Daybreak that most directly threatens existing security tooling vendor economics. Threat modeling, vulnerability triage, and patch validation are three of the most labor-intensive workflows in modern security operations. They are also three of the workflows least addressed by current security software. Most security teams run them as quarterly or annual exercises because they cannot afford to run them continuously.
If Codex Security delivers on the demonstrated workflow — scan codebase, validate highest-risk findings, fix them — at production scale, the procurement math for adjacent SAST, DAST, and SCA tools changes materially. The argument shifts from "we need a separate tool for each workflow" to "we need a frontier AI primitive that can run all three workflows agentically, plus the tools that integrate with it." That is the procurement reframe Daybreak partners are positioning for in advance. Snyk, Semgrep, Socket on the application security side are not betting that Codex Security replaces them. They are betting that Codex Security becomes the orchestration layer their tools plug into, and that integration is more valuable than independence.
What we do not yet have is independent benchmark data on Codex Security's accuracy. OpenAI's claim of 3,000 vulnerabilities fixed on GPT-5.4-Cyber is the company's own number. The Codex Security agent demonstration reported by Engadget is a curated demo. Production accuracy at scale, false positive rates on threat model generation, and time-to-fix metrics across heterogeneous codebases are all open questions. The next 90 days of partner case studies will answer those questions or expose the gap.
The 2026 cyber AI race — full timeline through May 11
The May 11 announcement does not stand alone. It is the culmination of a six-month sequence of cyber AI moves across the two leading frontier labs. Reading the timeline in order clarifies the bet each lab is making.
April 2026 — Anthropic Mythos preview ships. The more capable sibling to Opus 4.7 enters limited access, framed by Anthropic as exceeding the capability threshold where unrestricted release creates real-world risk. The Trusted Access ring is intentionally small. The safety-first framing is reinforced across Anthropic communications.
April 2026 — GPT-5.4-Cyber launches. OpenAI ships the first cyber-specialized variant of its agentic flagship. The model is positioned for vulnerability research, malware analysis, and red team workflows under Trusted Access gating. The public commitment metric — 3,000 vulnerabilities fixed in six weeks — anchors the credibility frame.
Early April 2026 — Mythos Discord breach on day one. Unauthorized Mercor contractor credentials surface inside an internal Anthropic Discord channel, exposing Mythos discussions. The incident hardens the Anthropic case that even tightly controlled access circles leak.
Late April 2026 — Sam Altman's fear-based marketing pivot. Altman publicly characterizes Anthropic's Mythos posture as bomb-shelter rhetoric, framing OpenAI's more permissive Trusted Access as the responsible alternative. The exchange marks the first time the two labs trade public positioning blows on cyber posture rather than capability claims.
Early May 2026 — Anthropic Claude Security public beta. Anthropic enters the vulnerability scanning market with Claude Security, directly threatening Snyk's product line and signaling that Anthropic intends to compete with category specialists rather than partner with them.
Early May 2026 — Claude-assisted Mexico water utility attack. Dragos publishes detailed analysis of an AI-assisted attack that compromised the country's third-largest water utility, with Claude generating 17,000 lines of malware and 195 million records exposed. The attack becomes both labs' favorite reference data point — for opposite arguments.
May 7, 2026 — GPT-5.5-Cyber general unlock. OpenAI opens GPT-5.5-Cyber to vetted cybersecurity teams globally under the Trusted Access for Cyber program, with phishing-resistant authentication required by June 1.
May 11, 2026 — OpenAI EU Cyber Action Plan. The European overlay launches, scoping Trusted Access to vetted EU partners, regulators, and the EU AI Office. CNBC reports talks with Anthropic over Mythos remain at "a different stage."
May 11, 2026 — Daybreak launches. The global umbrella initiative formalizes the partner coalition, introduces Codex Security, and frames the 20+ partner roster as the operational vehicle for the GPT-5.5 cyber stack worldwide.

The safety framing — trust, verification, proportional safeguards, accountability
OpenAI's public communications around Daybreak lean on a four-word safety frame — trust, verification, proportional safeguards, and accountability. The frame is not accidental. It is the linguistic counter to Anthropic's "capability threshold" framing for Mythos. Where Anthropic argues that some capabilities should be gated by a hard line, OpenAI argues that capabilities should be gated by a verification and accountability stack that scales with the access ring.
The operational substance behind the frame is what matters for procurement. Trust maps to the partner vetting model. Verification maps to the Trusted Access for Cyber program — applications, intended-use review, and security attestation. Proportional safeguards map to the Advanced Account Security requirement, phishing-resistant authentication by June 1, and the contractual usage perimeter. Accountability maps to the partner contracts themselves, which carry breach disclosure and incident response obligations that bilateral access to a model normally would not enforce.
Whether that frame holds in practice depends on enforcement. OpenAI has not yet published an annual transparency report on Trusted Access incidents, partner audits, or revocations. That report, when and if it materializes, will be the first real test of the proportional safeguards claim. Until then, the frame is a positioning statement supported by program structure but not yet by enforcement track record.
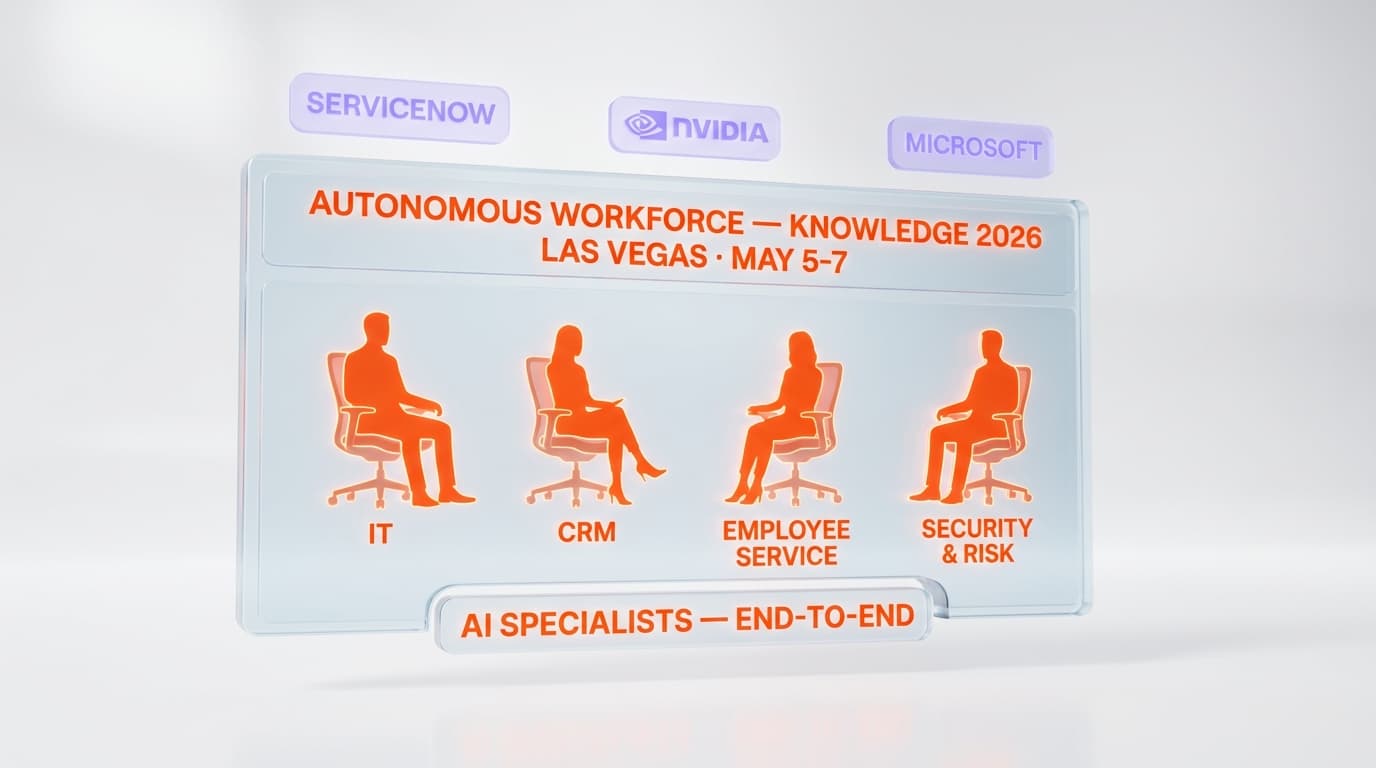
Who benefits — the mid-market security teams who have never had a threat modeler
The most immediate beneficiaries of Daybreak are not the Fortune 500 security teams who already have full SOC stacks, dedicated threat intel functions, and budgets for boutique red team engagements. Those teams will integrate the GPT-5.5 cyber surface through their existing vendor relationships and treat it as one more primitive in a stack they already operate at scale.
The teams that gain the most are the mid-market security organizations that have never had access to threat modeling expertise, that run vulnerability scans quarterly because continuous coverage was too expensive, and that have been outgunned on incident response by adversaries running AI-assisted offensive workflows since at least early 2025. Codex Security's autonomous threat modeling lowers the floor on what a mid-market team can do. A 12-person security team at a regional bank or a state government agency, with Codex Security integrated into their development pipeline, can run a continuous threat model that previously would have required a 40-hour consulting engagement once a year.
The Dragos report on the Mexico water utility makes the case viscerally. The country's third-largest water utility was compromised by AI-assisted offensive workflows, with 195 million records exposed. That utility likely did not have a dedicated threat modeler. It almost certainly did not have continuous vulnerability scanning at the depth required to catch the attack chain. Daybreak's bet is that the next utility in that position has Codex Security in production, that the next 17,000-line malware generation gets flagged before it lands, and that the partner integration coverage means the bet does not require every utility to negotiate a separate access deal with OpenAI to get the lift.
The risks — what could break Daybreak
No coalition strategy is risk-free. Daybreak's breadth-first approach carries three structural failure modes that the next 90 days of execution will either close or expose.
Failure mode one — partner integration depth versus marketing depth. A 20+ partner launch is straightforward to announce and harder to ship. If the named partners deliver press releases but not production integrations within the next two quarters, Daybreak risks reading as a marketing umbrella over a thin product surface. The Mythos and Glasswing posture, by contrast, ships with fewer partners but deeper integration commitments. The first verification of which approach wins will be the volume of partner-shipped Daybreak case studies by the end of Q3 2026.
Failure mode two — Codex Security accuracy at scale. The demonstration workflow — scan, validate, fix — is the most aspirational claim in the launch. Threat modeling generation, in particular, has a high false positive cost. A threat model with 30 percent noise is worse than no threat model, because it consumes scarce security analyst attention and trains the team to dismiss the tool. OpenAI has not yet published per-codebase accuracy metrics for Codex Security. Until those land, the agent layer is a promise rather than a proof.
Failure mode three — a single partner breach. The bigger the access ring, the higher the probability that one partner ships an integration that leaks usage data, exposes a model endpoint, or surfaces in an unauthorized adversarial workflow. A single Daybreak partner incident — particularly one involving offensive capability misuse — would be the empirical proof of the Mythos and Glasswing safety-first case. OpenAI has not yet faced that test under Daybreak's expanded coalition surface. Anthropic, by contrast, already faced the Mythos Discord incident on day one and updated its access posture accordingly.
What would prove Daybreak overhyped
This is the section we owe the analysis in honest framing. Daybreak is a strong launch on paper. The actual test is empirical, and the failure markers are knowable in advance.
Partner adoption rate below 50 percent shipping by Q4 2026. If fewer than half the named partners have publicly shipped Daybreak-integrated products by the end of the year, the coalition strategy underperformed the press cycle. The bar is not unreasonable — the named vendors are all established companies with engineering capacity to integrate a frontier AI primitive in two quarters if the integration is straightforward. Below 50 percent ship rate suggests either the integration friction was higher than advertised or the vendors hedged at announcement and walked back the commitment.
Vulnerability fix scale not exceeding 30,000 by year-end. OpenAI claims 3,000+ vulnerabilities fixed on GPT-5.4-Cyber across roughly six weeks of usage. Linear extrapolation puts the year-end number at well over 30,000 if usage compounds with the Daybreak partner expansion. If the year-end number lands materially below 30,000, either the 3,000 figure overcounted, the GPT-5.5 cyber surface did not lift usage as expected, or the partner integrations failed to drive incremental volume.
GPT-5.5 cyber benchmarks remain undisclosed. OpenAI published the GPT-5.5-Cyber CyberGym score in the May 7 unlock — 81.9 percent against base GPT-5.5 at 81.8 percent. Daybreak's GPT-5.5 Trusted Access for Cyber surface has not yet been benchmarked publicly on equivalent measures. If the benchmark gap between Daybreak's cyber model and the broader GPT-5.5 release is similarly narrow — under one percentage point — the marketing differentiation may exceed the capability differentiation. That gap matters for procurement decisions and for the credibility of the safety framing that treats the cyber variant as warranting a separate access ring.
A second high-profile partner breach or misuse incident. Anthropic's Mythos Discord breach hardened the closed-coalition argument. If Daybreak ships a comparable incident — an integration leak, a partner credential exposure, or a documented adversarial misuse case — the entire open coalition framing weakens materially. The risk is structural to the open-coalition strategy itself, not a function of execution quality. But it would shift the strategic gravity back toward Anthropic's posture within a single news cycle.

The strategic takeaway — May 11 redrew the AI cyber alliance map
The single most important thing about Daybreak is not the product surface. It is the formalization of the AI cyber alliance map. Before May 11, the structure was implicit. OpenAI was building broadly. Anthropic was building selectively. The split was visible in product decisions and partner choices but not yet codified in a coalition framework. After May 11, the split is codified. Daybreak is OpenAI's formal coalition. Glasswing plus Mythos is Anthropic's. The two coalitions will not converge — they are built on opposite priors about how cyber AI should ship at frontier capability levels.
For enterprise procurement teams, the practical implication is that the AI cyber primitive question now has a coalition dimension. Which lab's coalition you align with shapes which integrations you inherit, which contractual frameworks you accept, and which safety posture you adopt by association. Choosing Daybreak partners means accepting the open coalition philosophy and the partner vetting model as your safety backstop. Choosing Glasswing-aligned tools means accepting the closed elite philosophy and the smaller access ring as your safety backstop. Neither choice is wrong. Both choices have downstream consequences that compound with each integration.
For the labs themselves, the May 11 split establishes the empirical experiment. We will know, by the end of 2026, which coalition shipped more production cyber defense capability, which one experienced more partner-side incidents, and which one closed the offense-defense gap faster on the timelines that matter for critical infrastructure. The answer to that question will shape frontier AI cyber strategy for the rest of the decade. Daybreak is OpenAI's bet that breadth wins. Glasswing and Mythos are Anthropic's bet that selectivity wins. By December 31, 2026, the data will start to favor one side.
Frequently Asked Questions
What is OpenAI Daybreak?
OpenAI Daybreak is a global cybersecurity initiative announced on May 11, 2026 by OpenAI President Greg Brockman. It is built on GPT-5.5 with Trusted Access for Cyber and introduces Codex Security, an agentic security tool that performs autonomous threat modeling and vulnerability detection. Daybreak launched with 20+ partners including Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Akamai, Snyk, Trail of Bits, and SpecterOps. It is the global umbrella initiative; the OpenAI EU Cyber Action Plan announced the same day is the European regional overlay.
How is Daybreak different from the OpenAI EU Cyber Action Plan?
Daybreak is the global umbrella initiative. The OpenAI EU Cyber Action Plan, announced on the same day (May 11, 2026), is the European regional overlay scoped to vetted EU partners, regulators, and EU institutions including the EU AI Office. Daybreak covers global Trusted Access for Cyber program access through 20+ international partners. The EU Cyber Action Plan applies the same access model specifically to European cyber agencies, businesses, and governments.
Who are the Daybreak partners?
OpenAI announced 20+ partners at launch. The named partners include Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Akamai, Zscaler, Fortinet, Intel, Qualys, Rapid7, Tenable, Trail of Bits, SpecterOps, SentinelOne, Okta, Netskope, Snyk, Gen Digital, Semgrep, and Socket. The roster spans network and edge infrastructure, EDR/XDR, identity, vulnerability management, application security, hyperscaler-adjacent infrastructure, and specialized offensive security consulting.
What is Codex Security?
Codex Security is OpenAI's agentic security tool, built on Codex and announced as part of Daybreak. It has two core capabilities: it can automatically generate a threat model from an organization's codebase, and it can validate likely vulnerabilities and autonomously triage higher-risk findings. In OpenAI's launch demonstration reported by Engadget, Codex Security was tasked to scan a codebase, validate the highest-risk findings, and fix them — the full inner loop of defensive code maintenance compressed into an agentic workflow.
What are the five Daybreak use cases?
Per OpenAI's framing, GPT-5.5 with Trusted Access for Cyber is positioned for five named workflows: secure code review, vulnerability triage, malware analysis, detection engineering, and patch validation. Codex Security extends those workflows with autonomous threat modeling and agentic vulnerability remediation.
How does Daybreak compare to Anthropic Glasswing and Mythos?
Daybreak is the open coalition approach — 20+ partners, breadth-first integration strategy, Trusted Access for Cyber as the gating model. Anthropic Glasswing is the closed elite approach — four hyperscaler partners (Apple, Microsoft, Google, Amazon), narrow vetted access, more restrictive distribution of the Mythos preview model. The two coalitions are built on opposite priors about how frontier cyber AI should ship: OpenAI bets coalition breadth wins, Anthropic bets selectivity and safety controls win.
How many vulnerabilities has OpenAI's cyber AI actually fixed?
According to OpenAI's announcement, GPT-5.4-Cyber, the April 2026 foundation for Daybreak, has been used to fix more than 3,000 vulnerabilities since release. The number is OpenAI's own claim and has not yet been independently audited, and the company has not published a per-customer or per-CVE breakdown. Linear extrapolation across the year would put the figure well over 30,000 by year-end if Daybreak partner expansion drives usage growth as expected.
Why is Snyk on the Daybreak partner list?
Snyk is the most strategically interesting name on the Daybreak partner list because Anthropic Claude Security launched in early May 2026 as a direct competitive threat to Snyk's vulnerability scanning moat. One week later, Snyk joined Daybreak. The company is hedging both sides of the frontier AI cyber race — Anthropic competing with Snyk's product line directly, OpenAI inviting Snyk into the coalition. The contrast reveals the two lab coalition philosophies: OpenAI builds broad, Anthropic builds narrow.
What is Trusted Access for Cyber?
Trusted Access for Cyber is OpenAI's gating program for the GPT-5.5 cyber model surface. Vetted applicants submit credentials and intended-use information. Individual members must enable Advanced Account Security — phishing-resistant authentication, hardware-backed keys, or equivalent — by June 1, 2026. Organizations can attest to phishing-resistant single sign-on at the company level instead. The program is the safety perimeter underneath Daybreak's open coalition strategy.
What is the safety framing OpenAI uses for Daybreak?
OpenAI frames Daybreak around four safety principles: trust, verification, proportional safeguards, and accountability. Trust maps to partner vetting. Verification maps to the Trusted Access for Cyber application and attestation process. Proportional safeguards map to Advanced Account Security and contractual usage perimeters. Accountability maps to the partner contracts with breach disclosure and incident response obligations. The frame is the deliberate counter to Anthropic's capability-threshold framing for Mythos.
What would prove Daybreak overhyped?
Four failure markers are knowable in advance: (1) partner adoption rate below 50 percent shipping production integrations by Q4 2026; (2) total vulnerability fix scale not exceeding 30,000 by year-end; (3) GPT-5.5 Trusted Access for Cyber benchmarks staying undisclosed or revealing a sub-one-percentage-point gap with base GPT-5.5; (4) a high-profile partner breach or documented adversarial misuse case comparable to the Mythos Discord incident.
How does Daybreak affect mid-market security teams?
The most immediate beneficiaries are mid-market security organizations that have never had access to threat modeling expertise, that run vulnerability scans quarterly because continuous coverage was too expensive, and that have been outgunned by AI-assisted offensive workflows since 2025. Codex Security's autonomous threat modeling lowers the floor on what a 12-person security team at a regional bank or state government agency can run — turning a 40-hour annual consulting engagement into a continuous workflow integrated into the development pipeline.
Sources and references
- OpenAI Daybreak announcement page — openai.com/daybreak
- Decrypt coverage of OpenAI Daybreak launch — decrypt.co/367506/openai-launches-daybreak-ai-cybersecurity
- Engadget reporting on Daybreak partner list and Codex Security demonstration — engadget.com/2170410/daybreak-openai-cybersecurity-initiative
- MacRumors coverage of OpenAI Daybreak launch — macrumors.com/2026/05/11/openai-launches-daybreak
- Yahoo Finance coverage of OpenAI Daybreak initiative — ca.finance.yahoo.com/news/openai-unveils-daybreak-initiative-fortify-222409160
- Sister analysis on the OpenAI EU Cyber Action Plan — OpenAI EU Cyber Action Plan vs Anthropic Mythos
- Background on Anthropic Mythos preview — Anthropic Mythos preview: more powerful than Opus 4.7, limited access
- Mythos Discord breach context — Anthropic Mythos breach: Discord and Mercor unauthorized access
- Sam Altman framing on Mythos — Sam Altman: Anthropic Mythos as fear-based marketing
- Anthropic Claude Security and the Snyk angle — Anthropic Claude Security public beta — the Snyk attack angle
- The Dragos Mexico water utility incident — Claude-assisted Mexico water utility hack: 195M records exposed
- Trump White House FDA-style pre-release reviews — Trump White House AI pre-release review executive order
- Anthropic 10 GW compute empire context — Anthropic 10 gigawatts compute empire: the coding supremacy bet
- OpenAI's flagship LLM — ChatGPT
- Anthropic's flagship — Claude
- Mythos preview tool page — Claude Mythos preview